 本文由 创作,已纳入「FreeBuf原创奖励计划」,未授权禁止转载
本文由 创作,已纳入「FreeBuf原创奖励计划」,未授权禁止转载

关于WiFi-Pineapple-MK7_REST-Client
WiFi-Pineapple-MK7_REST-Client是一款功能强大的WiFi安全渗透测试工具,支持广大研究人员针对目标WiFi设备执行近距离的接入操作,并通过渗透测试等方法和主动/被动形式对目标设备执行安全检测,识别和分析存在安全漏洞或错误配置的无线接入点设备,以提升无线网络环境的安全性。
工具安装
广大研究人员可以直接使用下列命令将该项目源码克隆至本地:
git clone https://github.com/TW-D/WiFi-Pineapple-MK7_REST-Client.git
除此之外,我们在Debian、Ubuntu和Raspbian操作系统上也可以是你用下列命令来安装WiFi-Pineapple-MK7_REST-Client:
sudo apt-get install build-essential curl g++ ruby ruby-dev sudo gem install net-ssh rest-client tty-progressbar
Payload介绍
在项目的“./payloads/”目录下,你可以找到下列Payload:
命令和控制 | 开发者 | 使用样例 |
Hak5 Key Croc - 实时恢复键盘击键信息 | TW-D | (edit) ruby ./hak5_key-croc.rb |
Maltronics WiFi Deauther - 垃圾信标帧 | TW-D | (edit) ruby ./maltronics_wifi-deauther.rb |
安全防御 | 开发者 | 使用样例 |
Hak5 Pineapple Spotter | (edit) ruby ./hak5-pineapple_spotter.rb |
DoS | 开发者 | 使用样例 |
取消访问接入点的客户端身份验证 | TW-D | (edit) ruby ./deauthentication-clients.rb |
利用测试 | 开发者 | 使用样例 |
WPA测试接入点 | TW-D | (edit) ruby ./evil-wpa_access-point.rb |
伪造接入点 | TW-D | (edit) ruby ./fake_access-points.rb |
大量握手 | TW-D | (edit) ruby ./mass-handshakes.rb |
流氓接入点 | TW-D | (edit) ruby ./rogue_access-points.rb |
双接入点 | TW-D | (edit) ruby ./twin_access-points.rb |
通用 | 开发者 | 使用样例 |
系统状态、磁盘使用等 | TW-D | (edit) ruby ./dashboard-stats.rb |
网络接口 | TW-D | (edit) ruby ./networking-interfaces.rb |
系统日志 | TW-D | (edit) ruby ./system-logs.rb |
网络侦查 | 开发者 | 使用样例 |
2.4GHz 和5GHz 的接入点或客户端 | TW-D | (edit) ruby ./access-points_clients_5ghz.rb |
接入点或客户端 | TW-D | (edit) ruby ./access-points_clients.rb |
接入点MAC地址 | TW-D | (edit) ruby ./access-points_mac-addresses.rb |
接入点标记参数 | TW-D | (edit) ruby ./access-points_tagged-parameters.rb |
使用WiGLE收集访问接入点和无线网络映射 | TW-D | (edit) ruby ./access-points_wigle.rb |
客户端MAC地址 | TW-D | (edit) ruby ./clients_mac-addresses.rb |
开放访问接入点 | TW-D | (edit) ruby ./open_access-points.rb |
WEP 访问接入点 | TW-D | (edit) ruby ./wep_access-points.rb |
WPA 访问接入点 | TW-D | (edit) ruby ./wpa_access-points.rb |
WPA2 访问接入点 | TW-D | (edit) ruby ./wpa2_access-points.rb |
WPA3 访问接入点 | TW-D | (edit) ruby ./wpa3_access-points.rb |
其他 | 开发者 | 使用样例 |
针对2.4GHz和5GHz频段执行持续性网络侦查 | TW-D | (edit) ruby ./continuous-recon_5ghz.rb [CTRL+c] |
针对握手包执行持续性网络侦查 | TW-D | (edit) ruby ./continuous-recon_handshakes.rb [CTRL+c] |
持续性网络侦查 | TW-D | (edit) ruby ./continuous-recon.rb [CTRL+c] |
Payload开发样例
#
# Title: <TITLE>
#
# Description: <DESCRIPTION>
#
#
# Author: <AUTHOR>
# Version: <VERSION>
# Category: <CATEGORY>
#
# STATUS
# ======================
# <SHORT-DESCRIPTION> ... SETUP
# <SHORT-DESCRIPTION> ... ATTACK
# <SHORT-DESCRIPTION> ... SPECIAL
# <SHORT-DESCRIPTION> ... FINISH
# <SHORT-DESCRIPTION> ... CLEANUP
# <SHORT-DESCRIPTION> ... OFF
#
require_relative('<PATH-TO>/classes/PineappleMK7.rb')
system_authentication = PineappleMK7::System::Authentication.new
system_authentication.host = "<PINEAPPLE-IP-ADDRESS>"
system_authentication.port = 1471
system_authentication.mac = "<PINEAPPLE-MAC-ADDRESS>"
system_authentication.password = "<ROOT-ACCOUNT-PASSWORD>"
if (system_authentication.login)
led = PineappleMK7::System::LED.new
# SETUP
#
led.setup
#
# [...]
#
# ATTACK
#
led.attack
#
# [...]
#
# SPECIAL
#
led.special
#
# [...]
#
# FINISH
#
led.finish
#
# [...]
#
# CLEANUP
#
led.cleanup
#
# [...]
#
# OFF
#
led.off
end系统模块
身份认证访问/方法
system_authentication = PineappleMK7::System::Authentication.new system_authentication.host = (string) "<PINEAPPLE-IP-ADDRESS>" system_authentication.port = (integer) 1471 system_authentication.mac = (string) "<PINEAPPLE-MAC-ADDRESS>" system_authentication.password = (string) "<ROOT-ACCOUNT-PASSWORD>" system_authentication.login()
LED方法
led = PineappleMK7::System::LED.new led.setup() led.failed() led.attack() led.special() led.cleanup() led.finish() led.off()
Pineapple模块
仪表盘
通知方法:
dashboard_notifications = PineappleMK7::Modules::Dashboard::Notifications.new dashboard_notifications.clear()
统计方法:
dashboard_stats = PineappleMK7::Modules::Dashboard::Stats.new dashboard_stats.output()
日志记录
系统方法:
logging_system = PineappleMK7::Modules::Logging::System.new logging_system.output()
PineAP
客户端方法:
pineap_clients = PineappleMK7::Modules::PineAP::Clients.new pineap_clients.connected_clients() pineap_clients.previous_clients() pineap_clients.kick( (string) mac ) pineap_clients.clear_previous()
EvilWPA访问/方法:
evil_wpa = PineappleMK7::Modules::PineAP::EvilWPA.new evil_wpa.ssid = (string default:'PineAP_WPA') evil_wpa.bssid = (string default:'00:13:37:BE:EF:00') evil_wpa.auth = (string default:'psk2+ccmp') evil_wpa.password = (string default:'pineapplesareyummy') evil_wpa.hidden = (boolean default:false) evil_wpa.enabled = (boolean default:false) evil_wpa.capture_handshakes = (boolean default:false) evil_wpa.save()
过滤器方法:
pineap_filtering = PineappleMK7::Modules::PineAP::Filtering.new pineap_filtering.client_filter( (string) 'allow' | 'deny' ) pineap_filtering.add_client( (string) mac ) pineap_filtering.clear_clients() pineap_filtering.ssid_filter( (string) 'allow' | 'deny' )
身份伪造方法:
pineap_impersonation = PineappleMK7::Modules::PineAP::Impersonation.new pineap_impersonation.output() pineap_impersonation.add_ssid( (string) ssid ) pineap_impersonation.clear_pool()
设置访问/方法:
pineap_settings = PineappleMK7::Modules::PineAP::Settings.new pineap_settings.enablePineAP = (boolean default:true) pineap_settings.autostartPineAP = (boolean default:true) pineap_settings.armedPineAP = (boolean default:false) pineap_settings.ap_channel = (string default:'11') pineap_settings.karma = (boolean default:false) pineap_settings.logging = (boolean default:false) pineap_settings.connect_notifications = (boolean default:false) pineap_settings.disconnect_notifications = (boolean default:false) pineap_settings.capture_ssids = (boolean default:false) pineap_settings.beacon_responses = (boolean default:false) pineap_settings.broadcast_ssid_pool = (boolean default:false) pineap_settings.broadcast_ssid_pool_random = (boolean default:false) pineap_settings.pineap_mac = (string default:system_authentication.mac) pineap_settings.target_mac = (string default:'FF:FF:FF:FF:FF:FF') pineap_settings.beacon_response_interval = (string default:'NORMAL') pineap_settings.beacon_interval = (string default:'NORMAL') pineap_settings.save()
网络侦查
握手方法:
recon_handshakes = PineappleMK7::Modules::Recon::Handshakes.new recon_handshakes.start( (object) ap ) recon_handshakes.stop() recon_handshakes.output() recon_handshakes.download( (object) handshake, (string) destination ) recon_handshakes.clear()
扫描方法:
recon_scanning = PineappleMK7::Modules::Recon::Scanning.new recon_scanning.start( (integer) scan_time ) recon_scanning.start_continuous( (boolean) autoHandshake ) recon_scanning.stop_continuous() recon_scanning.output( (integer) scanID ) recon_scanning.tags( (object) ap ) recon_scanning.deauth_ap( (object) ap ) recon_scanning.delete( (integer) scanID )
设置
网络方法:
settings_networking = PineappleMK7::Modules::Settings::Networking.new settings_networking.interfaces() settings_networking.client_scan( (string) interface ) settings_networking.client_connect( (object) network, (string) interface ) settings_networking.client_disconnect( (string) interface ) settings_networking.recon_interface( (string) interface )
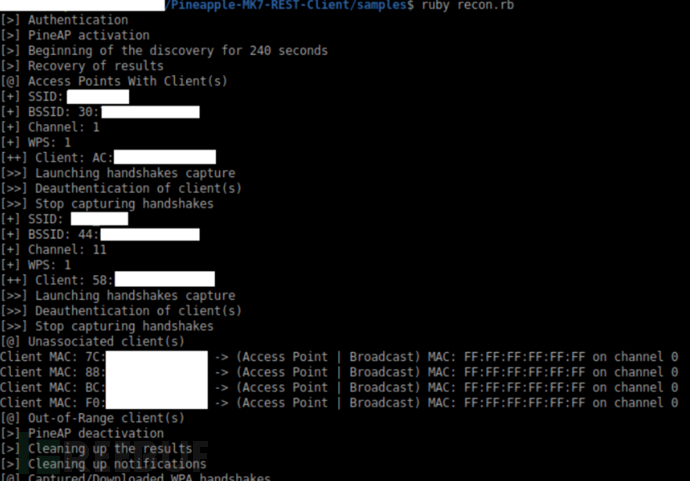
工具运行截图
项目地址
WiFi-Pineapple-MK7_REST-Client:【GitHub传送门】





